Portable Credentials
Evolution of Data Exchange Systems
The EDI Era
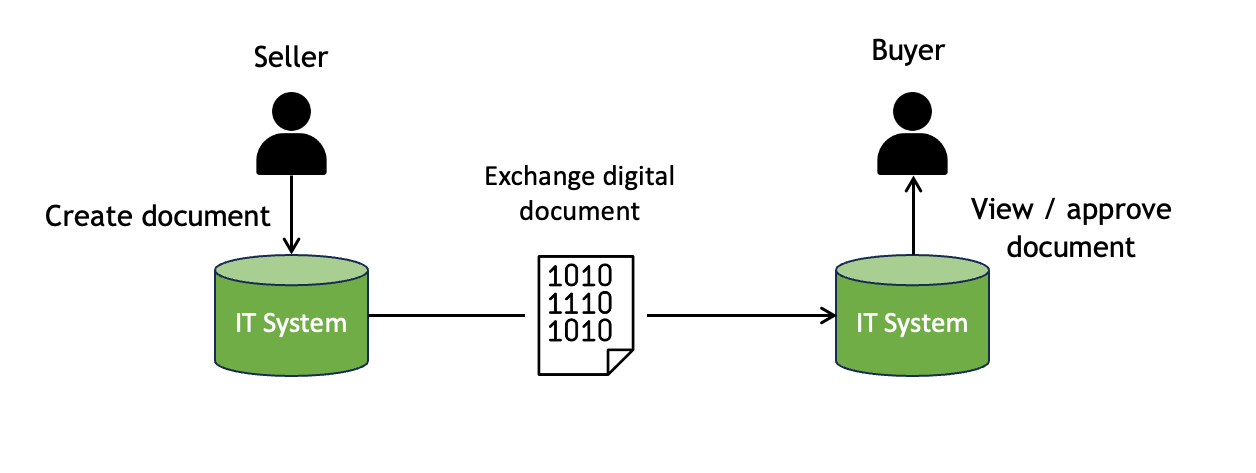
Electronic Data Interchange (EDI) promised to eliminate paper from trade. The concept is simple: connect two IT systems and exchange digital documents between them.
EDI started with ANSI X.12 in the late 1970s. UN/CEFACT released EDIFACT in the late 1980s. The internet and XML gave it a boost in the late 1990s. Regulatory mandates started from the late 2000s. Yet after 50 years of effort, only around 10% of cross-border trade is digitalized.
From Two Corners to Six
The simple point-to-point model quickly proved impractical. It’s too costly for every buyer and seller to build direct integrations with every counterparty. So the industry evolved through increasingly complex network models:
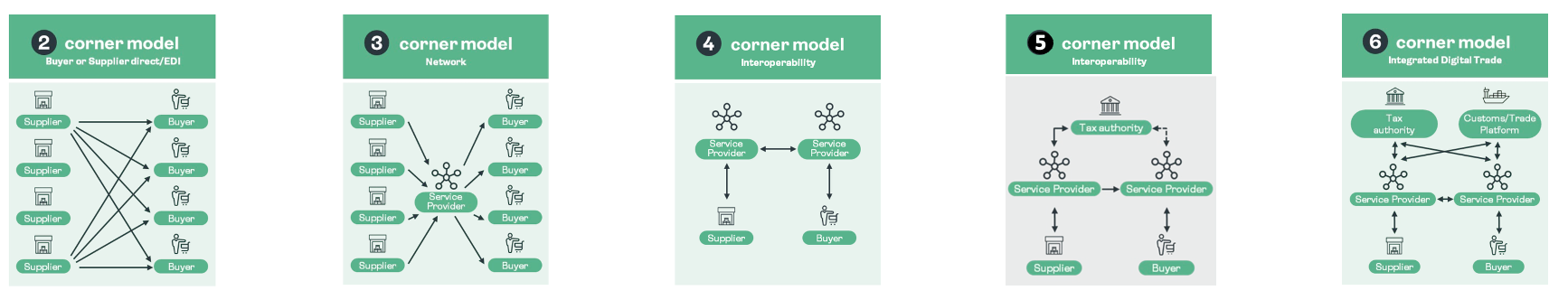
- 2-corner (direct EDI) — simple and secure, but costly to build many point-to-point integrations.
- 3-corner (network hub) — each party connects to one hub, but there are too many competing hubs.
- 4-corner (interoperability) — hubs connect to each other (like PEPPOL), but what about other parties like tax authorities?
- 5-corner (authorised observers) — includes regulators, but only works domestically.
- 6-corner (cross-border) — supports international flows, but becomes complex to govern and administer.
Each evolution added hubs. Each hub added cost and created a cyber-risk honeypot — a centralised store of valuable trade data that attracts attackers. And after all this, we are still at only 10% uptake.
Why These Approaches Failed to Scale
The fundamental problem is that a trade document does not flow between just two parties. A commercial invoice, for example, is used by the exporter, importer, banks, insurers, customs authorities in both countries, chambers of commerce, brokers, and freight forwarders.
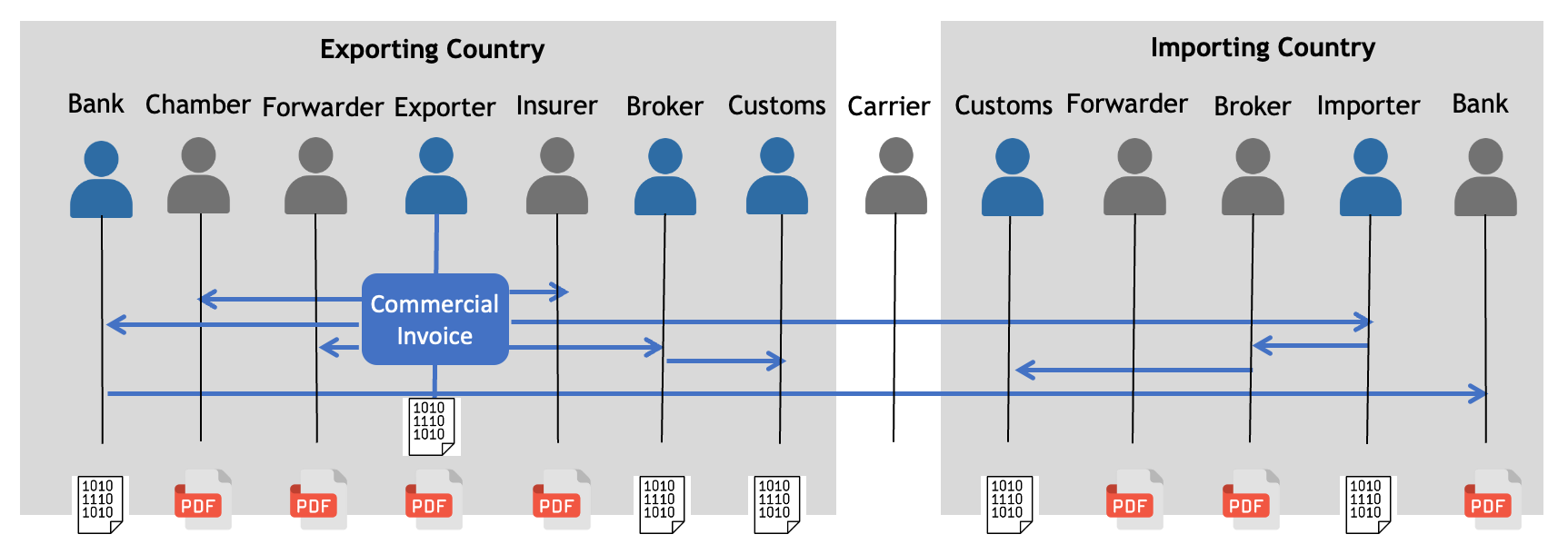
In almost every case, not all of these parties are on the same network. Some can process digital data (shown in blue above); others still rely on PDF or paper (shown in black). If traders must produce a PDF anyway to serve the unconnected parties, the incentive to invest in the digital network collapses.
The network never reaches everyone who needs the document. That is the core limitation.
Shifting Mental Models
Transport vs Payload
The hub-and-pipe model conflates two separate concerns: the transport (how data moves between systems) and the payload (the document itself). Every EDI standard defines both — you must join the network to use the document format.
But there is no reason the document must be bound to a specific transport. If the document itself carries proof of who issued it and that it hasn’t been tampered with, it can travel by any means — email, API, file transfer, USB drive, QR code — and still be trusted.
The Passport Example
This is not a theoretical idea. Everyone reading this has personally exchanged high-integrity digital data between complex IT systems across borders without any network of hubs and pipes.
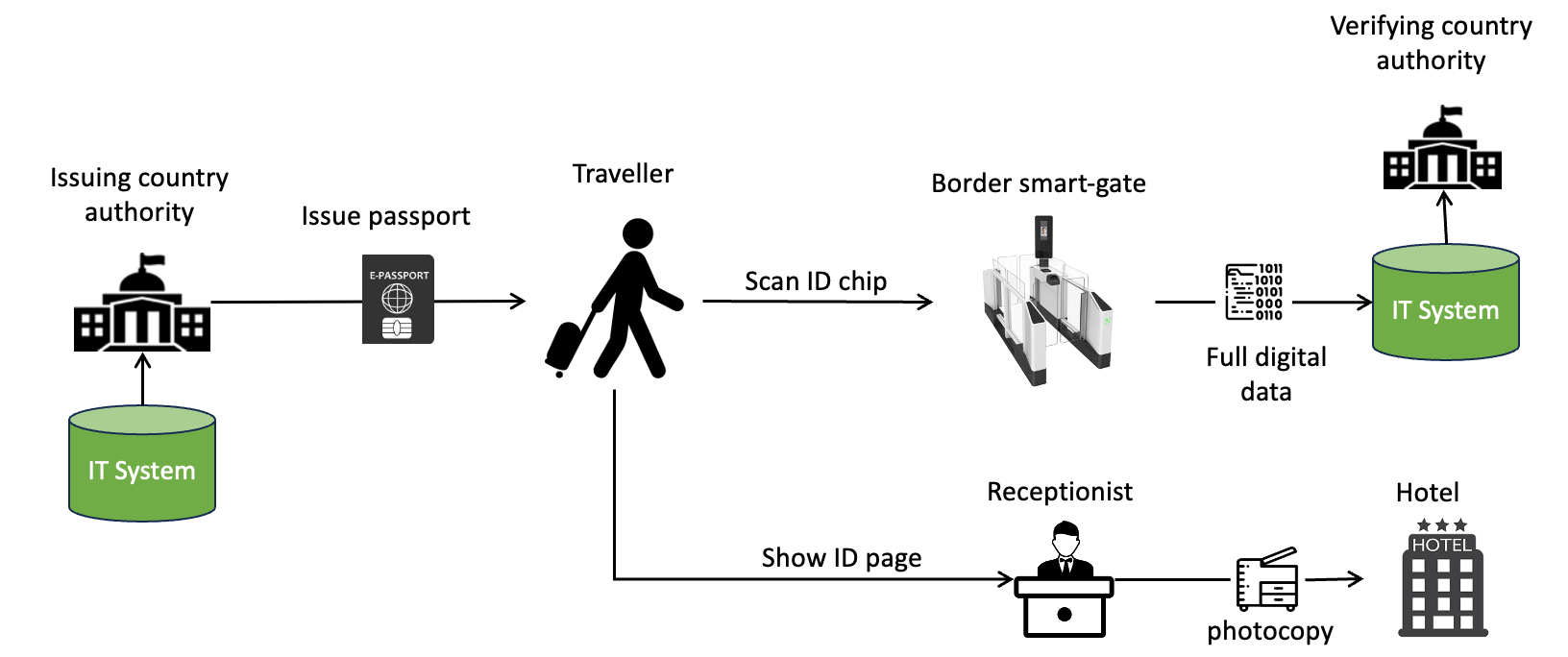
An e-passport is issued by one country’s authority and verified by another country’s border system — with no direct connection between the two IT systems. The traveller carries it. The border smart-gate scans the chip and gets full digital data. The hotel receptionist just looks at the ID page and takes a photocopy. Each country moved to e-passports in their own time, with no dependency on others.
Digital data went from issuing country system to destination country system with no direct connection. You carried it with you.
Structured Data in the AI Era
The rise of AI makes this shift even more important:
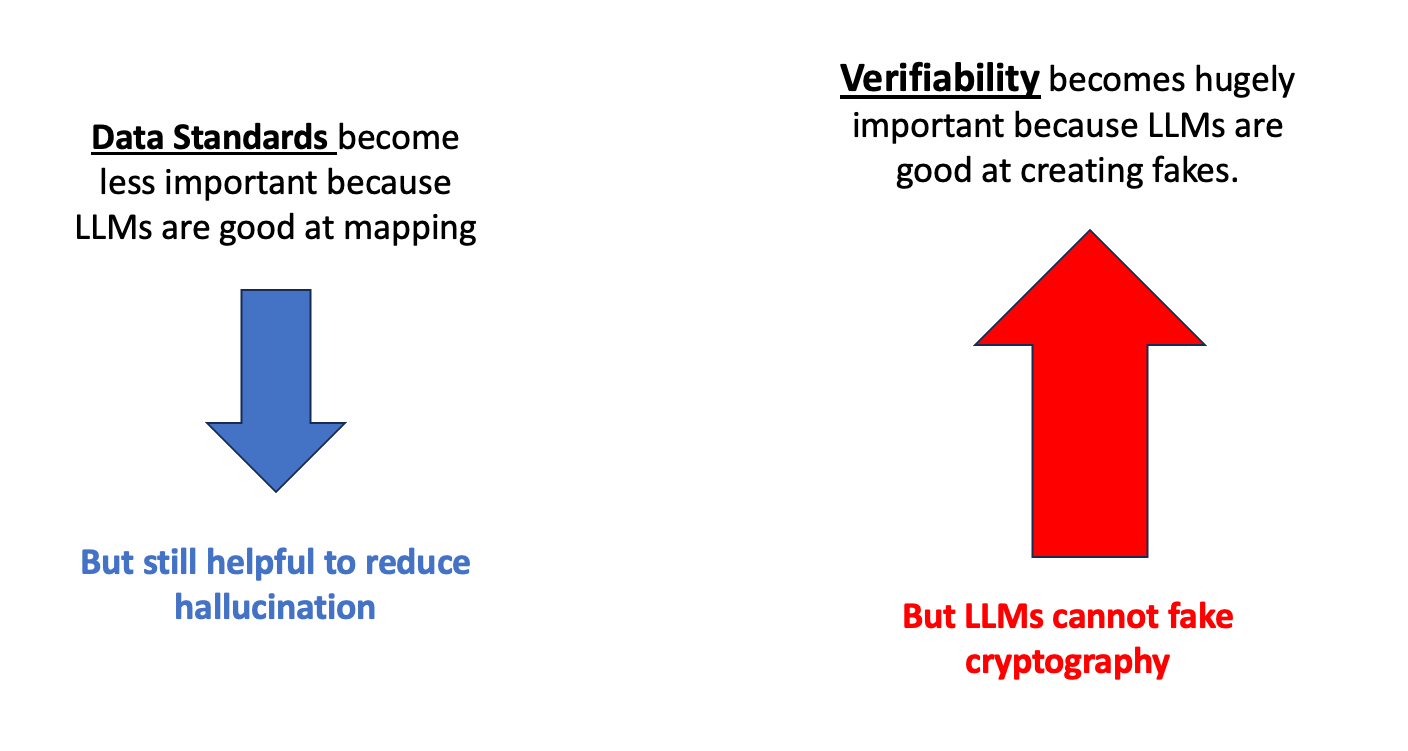
Data standards become less important because large language models are increasingly capable of mapping between different data formats. Standards still help reduce hallucination and ambiguity, but the hard requirement for identical formats between sender and receiver is softening.
Verifiability becomes hugely important because the same AI that can map data formats can also create convincing fakes. In an era where any document can be fabricated, cryptographic proof of origin and integrity is the only reliable defence. LLMs cannot fake cryptography.
New Mental Model: Exchange Without Networks
The Portable Credential Approach
When trade documents are represented as portable verifiable credentials — following the W3C standard — the passport model applies to trade:
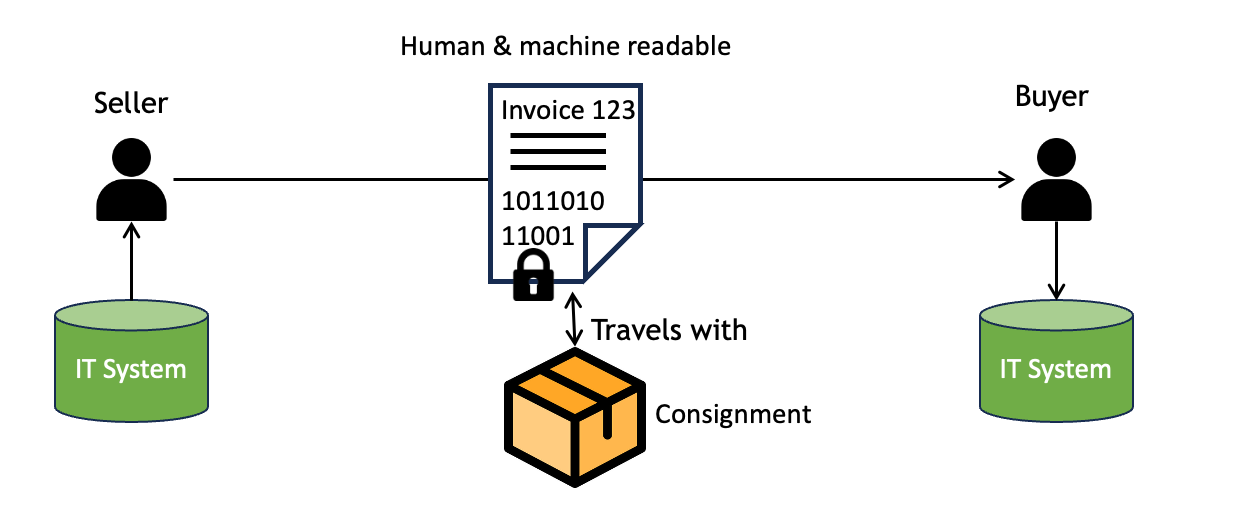
The document is both human and machine readable. It is cryptographically signed. It travels with the consignment. No network of hubs is needed.
This changes everything:
- Zero infrastructure cost — no hubs or intermediary platforms required.
- No cyber-risk honeypots — data is totally decentralised; there is no central store to attack.
- No counter-party dependency — implementation is easy because there’s no dependency on what the other party uses.
- Simple confidentiality — if you are given the data, you can access the data. No complex access control layers.
- Strong fraud resistance — identity integrity is much stronger than in network-based models.
The Commercial Invoice Example
The same verifiable document works for every party in the trade transaction. Those with digital capability process the structured data directly. Those without simply read the rendered document, just as they always have.
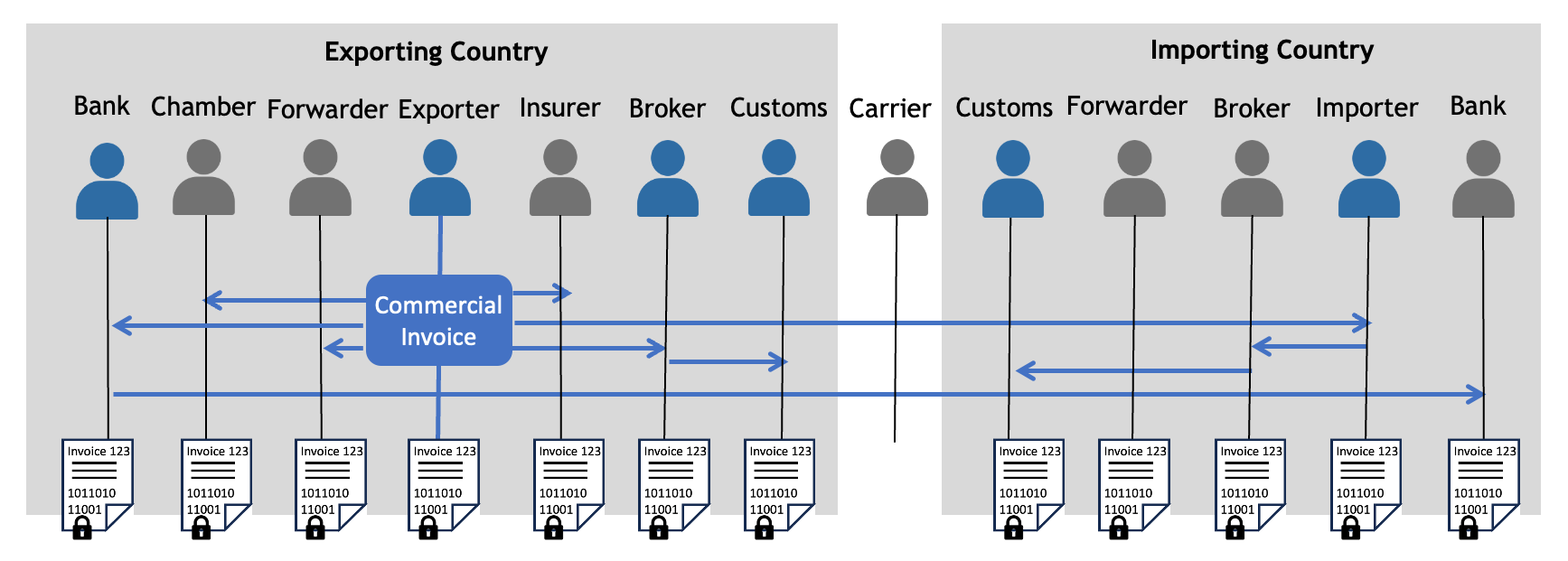
Every party — banks, chambers, forwarders, insurers, customs, brokers — gets the same document. No party is excluded because they aren’t on the right network. No party blocks another from participating.
This model is complementary to existing hub-and-pipe investments. Parties already connected through EDI or PEPPOL networks continue to benefit from those channels. But the same document also serves every party that isn’t on the network — which, in practice, is most of them.